Trezor Login: How to Access Your Hardware Wallet Safely (Beginner → Mid-Level)
Step-by-step guidance on Trezor login flows, secure habits before entering seeds, troubleshooting, and advanced tips for users who care about real security.
Why "Trezor login" is not like a normal website login
When people search for “Trezor login”, they’re usually expecting a simple username/password page. Cryptocurrency security doesn’t work that way. With Trezor — a hardware wallet — “logging in” involves a combination of a physical device, a PIN, and sometimes a passphrase. The crucial difference: your private keys stay offline on the hardware device. That makes the login process inherently safer, but also slightly different from the usual web logins you’re used to.
Before we dive into exact steps for a Trezor login, let’s cover the mindset: you are not trusting a website with your keys; you are using a local device to authorize transactions and view balances. Treat the Trezor login as an on-device confirmation workflow — not just a password entry.
Quick overview: Typical Trezor login flows
There are two common scenarios where people mean "Trezor login":
- Accessing Trezor via Trezor Suite: You connect your device to Trezor Suite (desktop or web) and enter the device PIN when prompted. The Suite displays balances and allows you to create or sign transactions.
- Using Trezor with third-party wallets: You connect the Trezor, the third-party wallet recognizes it as a hardware key, and you confirm actions on the device itself. Examples include Electrum, MyCrypto, and some DeFi web apps.
In both flows, actual authorization happens physically on the Trezor device. Think of the device as the gatekeeper — the "login" on your screen is only a partial step.
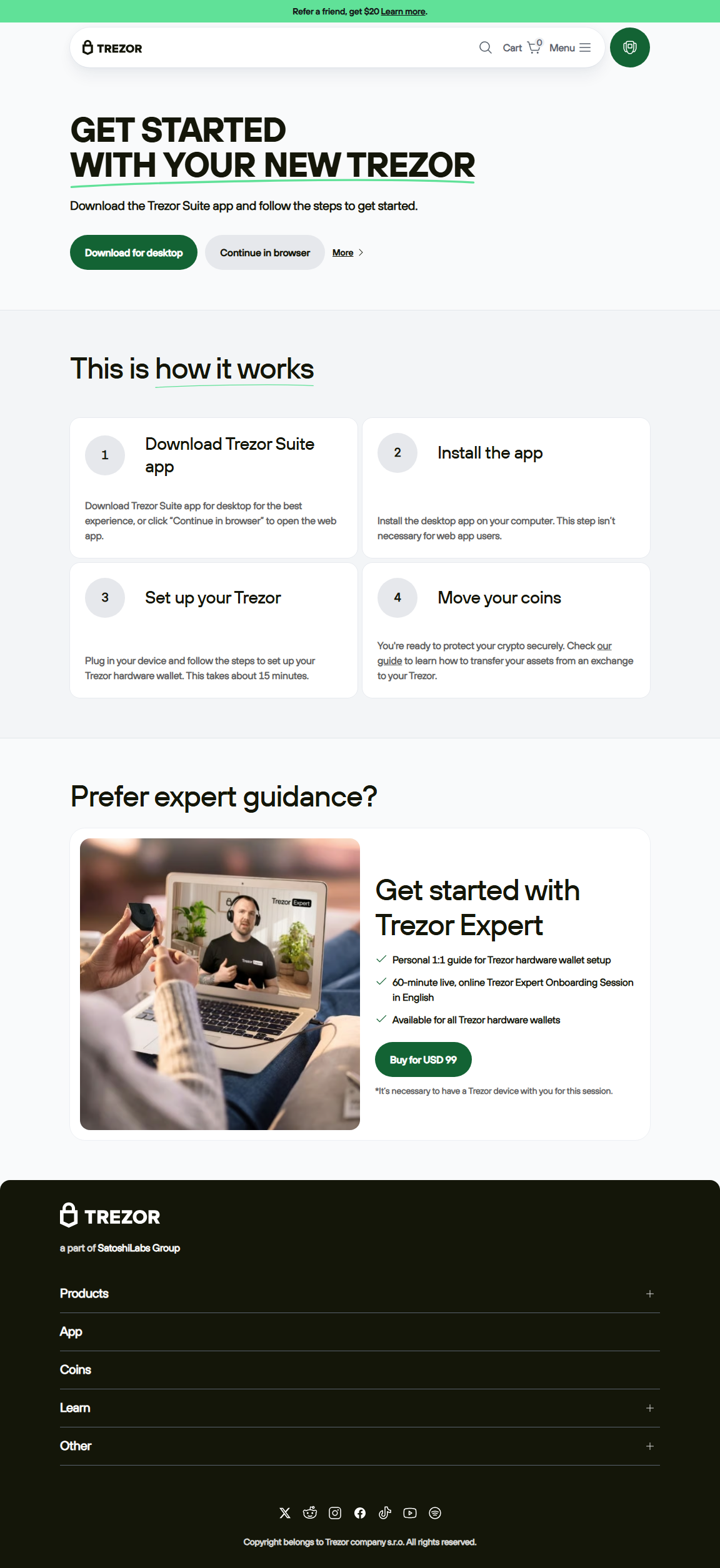
Step-by-step: Secure Trezor login with Trezor Suite (recommended)
This is the recommended, official way to manage most accounts: use Trezor Suite with your hardware device.
1. Prepare your environment
Before you connect your Trezor, make sure your computer is trusted: no suspicious browser extensions, updated OS, and preferably a machine you control. Close unnecessary apps and avoid public Wi-Fi. Physical privacy matters too — don't set up or log in while others can see your screen or device.
2. Connect your Trezor and open Trezor Suite
Connect via the supplied USB cable. Open the Suite application on your computer. The Suite will detect the device and show a brief onboarding screen. If the Suite asks for a firmware update, follow official prompts — but do not install firmware from any third-party source.
3. Enter your device PIN
The Suite will prompt you to enter a PIN on the computer, but you must confirm the digits on the Trezor device screen. That prevents malicious software from intercepting your PIN entry. Never enter your recovery seed — only the PIN — during login.
4. Confirm login / view account
Once the device validates the PIN, Trezor Suite unlocks a view-only session: you can view balances and create transactions. Any transaction that moves funds requires you to confirm details on the device's screen.
5. Sign out and safely disconnect
When you’re done, close the Suite, and physically disconnect the Trezor. For added safety, reboot your machine occasionally after major operations if you suspect anything unusual.
Key safety rules BEFORE you ever enter a seed or perform a Trezor login
Many mistakes happen before the login. These rules protect you from phishing, scams, and accidental loss:
- Never enter your recovery seed on a website: Your seed belongs only on the physical Trezor device and written backups (paper/metal). Any website asking for the seed is malicious.
- Only use official software: Use the official Trezor Suite (download from the device packaging instructions) or verify the application via the device’s manufactures instructions. Avoid unverified "login" pages claiming to be Trezor.
- Verify your device: When you first set up a Trezor, the device screen will show a randomized seed generation and verification. If the device behaves differently, stop immediately.
- Check URLs and emails closely: Phishing is often subtle — small character changes in domain names or lookalike pages are common.
Troubleshooting common "Trezor login" issues
Device not detected
First, try a different USB cable and port. Avoid USB hubs if possible. Make sure the device screen lights up — if it doesn't, the cable or device may be faulty. Restart your computer and retry.
PIN not accepted
Remember the Trezor PIN is entered indirectly: the Suite shows a randomized keypad and you press corresponding numbers on the device. If you enter the wrong PIN multiple times, the device enforces delays to hamper brute-force attempts. If you truly forgot your PIN, only the recovery seed can restore access on a new device.
Browser or Suite errors
Confirm you’re running the latest version of Trezor Suite and that your browser is up to date. Clear cache if necessary. If errors persist, check official community resources or contact official support, but never disclose your seed or PIN in support requests.
Using "Trezor login" with third-party apps and DeFi
Many advanced users connect Trezor to wallet apps and DeFi platforms. The flow usually works like this: the website requests wallet access, the third-party wallet passes a request to your Trezor, and you approve the request on the device. Important caveats:
- Always review exact transaction details shown on the Trezor screen — including destination addresses and amounts.
- When interacting with smart contracts, be careful: approving a contract can grant long-lived permissions. Use tools to limit allowances where possible.
- Prefer hardware-signing via Trezor for high-value operations; avoid signing unnecessary transactions.
Because you're using a hardware key, even compromised web code cannot move funds without your device's physical confirmation — but it can trick you into approving harmful permissions if you don’t review the on-device prompts carefully.
Advanced: Passphrases, hidden wallets, and recovery
For users who want stronger protection, Trezor supports optional passphrases. A passphrase is effectively an additional word appended to your recovery seed, creating a different wallet. Important notes:
- A passphrase can protect against someone who finds your seed, but if you forget the passphrase, funds are irretrievable.
- Use a memorable but strong passphrase; consider using a manager for a hint system rather than the passphrase itself.
- Hidden wallets: with passphrases you can create multiple hidden wallets using the same physical seed.
Always practice with small amounts before using passphrases for large holdings.
Real-world analogies to understand Trezor login
Analogy helps: imagine a bank safety deposit box. The bank (website) provides the lobby and staff; the key to your box is your physical Trezor. You can go to the bank (Trezor Suite) and request access, but the bank can’t open the box without your physical key and approval. The recovery seed is the emergency key stored separately — useful only if the physical key is lost.
This analogy clarifies why you should trust the device and not external websites with critical secrets.
Checklist: Safe Trezor login every time
- Use a trusted computer and private network.
- Verify you are using the official Trezor Suite or a vetted third-party wallet.
- Confirm device firmware is official (via on-device prompts).
- Enter PIN and confirm any transaction directly on the Trezor screen.
- Never enter your recovery seed on any website or share it.
- Log out and disconnect after use.
FAQ — Quick answers to common "trezor login" questions
- Q: Can I "log in" to Trezor from any computer?
- A: Yes — the device is portable. You can connect to Trezor Suite on another computer and restore access with your PIN and/or recovery seed. But only use trusted machines.
- Q: Does Trezor have a username/password web login?
- A: No. Trezor relies on the physical device plus PIN/passphrase. There’s no central account system with a username/password like traditional websites.
- Q: What should I do if my device prompts for firmware update during login?
- A: Follow official prompts within Trezor Suite. Firmware updates often fix security issues — but only install updates that the device or official software recommends. Do not approve updates from unverified sources.
- Q: Is it safe to use Trezor for DeFi?
- A: With caution. Trezor can be used for DeFi, but always review contract approvals carefully and use hardware signing to reduce risk. Consider using intermediary wallets for complex interactions.
Closing thoughts
The phrase "trezor login" may make you think of a quick username and password, but the reality is far more secure: hardware-based authentication, physical confirmation, and an emphasis on keeping your secret keys offline. Learning the right habits — never sharing your seed, verifying transactions, and using the official Trezor flows — gives you control and peace of mind.
Take time to practice the login process with small transactions until it becomes second nature. Security is a habit; repeatable, careful actions are what protect real assets over time.
Disclaimer: This is not an official Trezor site. This content is provided solely for educational and informational purposes. Never enter your recovery seed, PIN, or passphrase on unofficial websites or share them with anyone. Make sure to verify device prompts and official software before performing any sensitive actions.